Post-Quantum Migration: How to Future‑Proof Your Document Signing with QuickSign
Prepare for tomorrow’s threats today. Explore post-quantum migration and learn how QuickSign future‑proofs your document signing against quantum attacks.

Post-Quantum Migration: How to Future‑Proof Your Document Signing with QuickSign
Why Post-Quantum Migration Matters for Business Document Signing

The way your business signs contracts, NDAs, and agreements today may not be secure tomorrow. Quantum computers are expected to break widely used cryptographic algorithms such as RSA and elliptic curve cryptography (ECC), the backbone of most current digital signatures and secure connections. While large-scale quantum computers are still emerging, regulators and standards bodies have already moved: in August 2024, NIST published its first three post-quantum cryptography (PQC) standards (FIPS 203, 204, 205) to protect encryption and digital signatures against quantum attacks. (csrc.nist.gov)
For any organization that sends, signs, and stores sensitive documents, this is not an abstract research topic. It’s a concrete roadmap problem: how do you migrate your document signing workflows to post-quantum-safe systems without disrupting business?
This is where a modern e‑signature platform like QuickSign becomes strategic. QuickSign combines AI document generation, simple drag‑and‑drop signing workflows, and a modern architecture that can evolve with PQC standards—so your migration to quantum‑resistant signing can be planned, not rushed.
Key takeaway: Post‑quantum migration is about more than “new crypto.” It’s about choosing document signing tools, like QuickSign, that can adapt as PQC standards evolve—without forcing you to rebuild your workflows later.

What Is Post-Quantum Migration?
Post‑quantum migration is the process of transitioning your systems from classical cryptography (RSA, ECC) to quantum‑resistant algorithms that can withstand attacks from future quantum computers. For document signing, this primarily affects:
- How documents are signed and verified (digital signature algorithms).
- How documents are transferred and stored securely (encryption and key exchange).
NIST’s PQC program has selected and standardized algorithms to replace today’s vulnerable ones. For example: (csrc.nist.gov)
- ML‑KEM (FIPS 203) – based on CRYSTALS‑Kyber, for key establishment and general encryption.
- ML‑DSA (FIPS 204) – based on CRYSTALS‑Dilithium, for digital signatures.
- SLH‑DSA (FIPS 205) – based on SPHINCS+, a hash‑based backup digital signature scheme.
- FALCON / FN‑DSA (FIPS 206, in development) – an additional lattice‑based signature scheme. (nist.gov)
- HQC – selected in March 2025 as a backup key‑encapsulation mechanism alongside ML‑KEM. (csrc.nist.gov)
Post‑quantum migration means mapping where you use crypto today, planning how to replace it with these new standards, and choosing vendors who are “crypto‑agile”—able to upgrade cryptography under the hood without breaking your user experience.
The “Harvest Now, Decrypt Later” Risk
One reason experts urge organizations to start planning now is the “harvest now, decrypt later” threat. Adversaries can intercept and store encrypted traffic or signed documents today, then decrypt or forge them once quantum computers are strong enough to break RSA/ECC. Data with long confidentiality lifetimes—contracts, IP, personal records—are especially vulnerable. (techradar.com)
For businesses using e‑signatures, that means:
- Long‑term contracts might be exposed or repudiated in the future if signatures rely on algorithms that later become breakable.
- Archived signed documents could lose their evidentiary value if their
cryptographic protections are no longer considered secure.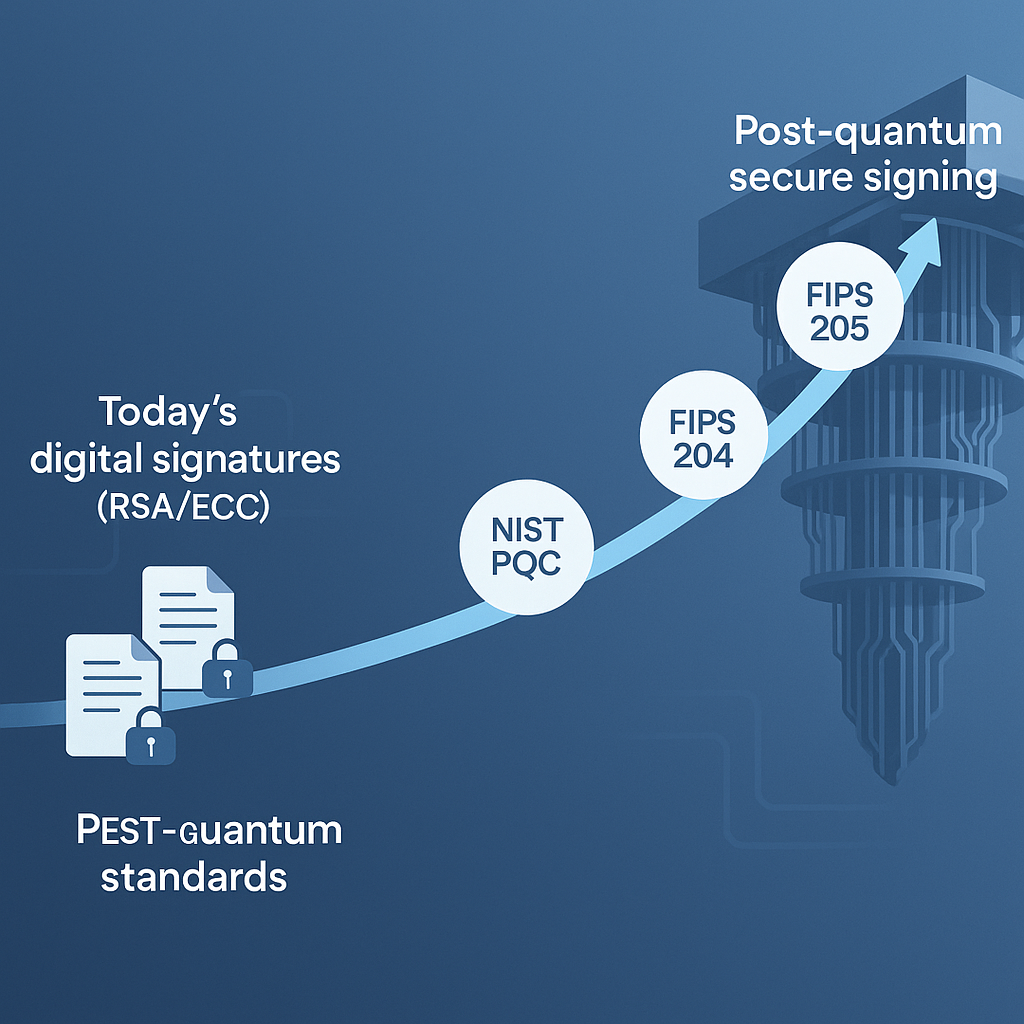
By selecting a platform like QuickSign that is designed to follow NIST PQC standards, you reduce the risk that today’s agreements become tomorrow’s liabilities.
How PQC Affects Digital Signatures and E‑Signature Platforms
In the context of document signing, post‑quantum migration affects two layers:
- Transport and storage security – how documents move between you, your signers, and the platform.
- Signature integrity and non‑repudiation – how the “who signed what, and when” evidence holds up over time.
From RSA/ECC to Post‑Quantum Algorithms
Today, many digital signature schemes for documents rely on RSA or ECDSA. These are vulnerable to Shor’s algorithm on a sufficiently powerful quantum computer. NIST’s PQC standards specify modern replacements like ML‑DSA and SLH‑DSA aimed precisely at digital signing scenarios: software, certificates—and critically, documents. (nist.gov)
A future‑ready platform such as QuickSign can:
- Use post‑quantum TLS (e.g., ML‑KEM‑based key exchange) as browsers and libraries adopt it.
- Adopt PQC‑backed digital signatures for internal evidence and audit trails as standards and tooling mature.
From a business user’s perspective, the interface doesn’t need to change. You still drag, drop, and send for signature. But under the hood, the cryptographic primitives evolve in line with NIST guidance.
Crypto‑Agility: The Hidden Requirement
Experts stress that PQC migration will be a multi‑year, staged process, requiring organizations to build “crypto‑agility”—the ability to replace cryptographic algorithms without redesigning entire systems. (techradar.com)
QuickSign is built with this in mind. Instead of locking customers into fixed, legacy stacks, QuickSign’s modern, cloud‑native architecture is designed to:
- Abstract cryptography behind services that can be upgraded as PQC libraries and standards evolve.
- Maintain stable APIs and workflows for your teams (upload, place fields, send, track) as cryptographic layers change underneath.
- Support layered security; for example, using both classical and PQC algorithms in hybrid modes during transition periods, as many industry roadmaps recommend. (postquantum.com)
Pro tip: When evaluating e‑signature tools for post‑quantum readiness, ask how they plan to adopt NIST PQC algorithms (ML‑KEM, ML‑DSA, SLH‑DSA) and whether they support hybrid “classical + PQC” modes during migration. Platforms like QuickSign that emphasize agility are far easier to future‑proof.
A Practical Roadmap to Post‑Quantum Migration for Document Signing
Most organizations don’t need to become cryptography experts to migrate. But you do need a structured approach and the right vendors. Here’s a practical roadmap tailored to your document signing stack and how QuickSign can support each step.
1. Take Inventory of Your Document Workflows
Start by mapping where and how you use e‑signatures today:
- What types of documents? (e.g., sales contracts, HR agreements, NDAs, vendor contracts).
- Which departments rely on them? (legal, HR, procurement, sales).
- How long do these documents need to remain valid and confidential?
With QuickSign’s AI Document Generation, you can standardize these workflows more quickly. Instead of hunting through old templates, you can:
- Describe the agreement you need in plain language (e.g., “Mutual NDA for a US software company, 2‑year term, covers source code and customer data”).
- Have QuickSign generate a draft NDA automatically.
- Save it as a reusable template for future, PQC‑ready signing flows.
This catalog of standardized, AI‑generated documents becomes the backbone of your migration: you know what you sign, how often, and how long each document matters.
2. Classify Long‑Lived and High‑Value Documents
Next, focus on documents that:
- Contain sensitive IP or regulated data.
- Have long legal or commercial lifetimes (e.g., 7–20 years).
- Are critical for audits, disputes, or compliance.
These are the prime targets for early post‑quantum protection because they’re most at risk from “harvest now, decrypt later” strategies. (techradar.com)
Within QuickSign, you can organize these contracts into dedicated workspaces or folders and apply stricter policies (e.g., internal approvals before sending). As PQC support becomes available, you can prioritize migration for these collections first.
3. Choose a PQ‑Ready E‑Signature Platform
Traditional, per‑seat e‑signature solutions often carry legacy architectures and pricing that make long‑term migration expensive and inflexible. Unlike traditional per‑seat solutions, QuickSign offers flat‑rate pricing at $15/month for your entire team, which means you can involve more stakeholders (legal, IT, security, compliance) in the migration process without worrying about license sprawl.
When evaluating platforms, consider:
- Architecture: Is the vendor already talking about PQC and crypto‑agility?
- Standards alignment: Are they tracking NIST PQC standards and planning to adopt ML‑KEM, ML‑DSA, and SLH‑DSA?
- Audit trails: Do they provide strong, exportable evidence records that can be anchored to new cryptographic proof schemes over time?
QuickSign is purpose‑built for this kind of evolution. You get:
- Drag‑and‑drop field placement to keep signer experience simple, regardless of cryptographic layer.
- Real‑time tracking to monitor who opened, viewed, and signed each document—essential metadata for long‑term evidentiary value.
- Seamless sending, so business users don’t have to think about “PQC vs. non‑PQC”—they just send, and the platform handles the security details.
4. Modernize Templates and Automate Where Possible
Once your core workflows are identified, use QuickSign’s AI to modernize and standardize them. A typical migration sequence could be:
- Upload your legacy Word/PDF contracts into QuickSign.
- Use AI Document Generation to:
- Refresh outdated language (e.g., data protection terms) to reflect current best practices.
- Generate missing agreements (like DPAs or updated NDAs) that were previously handled ad hoc.
- Convert these into QuickSign templates with:
- Drag‑and‑drop signature, date, and initial fields placed once.
- Saved recipient roles (e.g., “Customer,” “Vendor,” “Employee”).
As PQC support becomes available in the platform’s backend, all documents using these templates benefit automatically—no need to redesign each workflow.
5. Plan for Hybrid Cryptography During Transition
Industry guidance suggests that many systems will run in hybrid mode during migration: combining a classical algorithm (like ECDSA) with a PQC algorithm (like ML‑DSA) to hedge against unforeseen weaknesses in either. (postquantum.com)
In practice, this might look like:
- Your e‑signature platform securing connections with a TLS stack that uses both ECDHE and ML‑KEM key exchange.
- Document evidence being anchored in logs or ledgers that use a combination of classical and PQC signatures.
Because QuickSign abstracts these details away from end users, your legal and business teams don’t need to wrestle with crypto options. As hybrid modes become the norm at the infrastructure level, QuickSign can adopt them while keeping your day‑to‑day workflows unchanged.
6. Test, Monitor, and Educate Your Teams
Finally, successful migration depends on people understanding what’s changing and what’s not. With QuickSign, you can:
- Run pilot projects where a subset of contracts are executed using the latest security features.
- Use real‑time tracking to confirm that signers are completing PQC‑secured flows without friction.
- Export audit trails to demonstrate to auditors or regulators that your signing processes align with modern cryptographic guidance.
Because QuickSign’s interface remains familiar—upload, drag fields, add recipients, send—training is lightweight. Most of your communication can focus on why you’re upgrading security, not how to use a new tool.
Learning More: Recommended Post‑Quantum Cryptography Resources
If you’d like to go deeper into PQC and migration strategies, these video resources provide approachable overviews that complement what you’re doing with QuickSign:
Overview of Post‑Quantum Cryptography
Post‑Quantum Cryptography: the Good, the Bad, and the Powerful
This talk provides a balanced view of PQC: why it’s needed, what’s promising, and where challenges remain. As you think about e‑signature migration, it helps frame why standards like ML‑KEM and ML‑DSA matter for everyday business security.
Roadmap‑Focused PQC Migration Content
Roadmap to PQC (Post Quantum Cryptography) Migration by QNu Labs
This video discusses high‑level migration roadmaps—inventory, prioritization, and phased rollout—which map closely to how you can structure your transition using QuickSign as your central document signing hub.
Foundations of PQC
Post Quantum Cryptography (PQC) | Part‑1: Introduction
If your legal or IT stakeholders are new to PQC, this introduction is a good shared starting point before you align on a migration plan that includes upgrading your e‑signature stack with QuickSign.
Example: A Post‑Quantum‑Aware Contract Workflow with QuickSign
To make this concrete, here’s what a future‑ready contract workflow might look like for a mid‑sized SaaS company adopting QuickSign as its main signing platform.
Step 1: Generate a PQ‑Aware NDA Template
- Legal opens QuickSign and uses AI Document Generation to draft a mutual NDA that:
- Includes modern data protection and security language.
- References secure digital execution via a compliant e‑signature platform.
- The NDA is saved as a template, with:
- Signature, date, and initial fields placed using drag‑and‑drop.
- “Company” and “Counterparty” roles pre‑configured.
Step 2: Send for Signature in Under 60 Seconds
- A sales rep selects the NDA template in QuickSign.
- They add the prospect’s email and name; thanks to seamless sending, the whole process—from choosing the template to clicking “Send”—takes under a minute.
- QuickSign handles secure delivery and tracking, and, as PQC support is rolled out in the platform, the underlying cryptographic protocols protecting this flow will be upgraded automatically.
Step 3: Track, Archive, and Prove
- Legal and sales teams use real‑time tracking to see when the NDA is opened and signed.
- The final, signed NDA is stored with a detailed audit trail (timestamps, IP addresses, signer actions).
- As post‑quantum algorithms become standard in TLS and digital signatures, QuickSign’s back‑end can re‑anchor evidence or incorporate PQC‑based signatures into these audit trails—maintaining the long‑term validity of the agreement.
The key benefit: your organization doesn’t need to rewrite internal playbooks every time cryptography evolves. By centralizing document signing on QuickSign, your contracts inherit the platform’s security roadmap.
Cost‑Effective Post‑Quantum Readiness with QuickSign
Security transformations are often slowed by cost and licensing constraints. QuickSign is intentionally structured to remove those barriers:
- Generous free tier: Generate 2 documents and send 1 document to unlimited recipients—ideal for piloting PQ‑ready workflows.
- Affordable flat‑rate pricing: At just $15/month for your whole team, you can include legal, IT, security, and business users without worrying about per‑seat fees.
- Scalable workflows: From one‑off NDAs to large‑scale HR rollouts, the same PQ‑aware infrastructure can support your growth.
This means you can start your post‑quantum migration planning now—standardizing templates, modernizing workflows, and consolidating signing on a single platform—without needing a large up‑front investment.
Ready to simplify your document signing? Try QuickSign for free - generate 2 documents and send 1 document to unlimited recipients at no cost. No credit card required.